Confusion over responsibility for a data breach, and hackers taking from other hackers? Sounds like a bad (or good) sitcom.
First we get news of ShinyHunters, back once more, pulling off a breach of Instructure Canvas, a Utah-based learning management systems used by tens of millions of educators and students worldwide for distributing coursework, recording grades, and facilitating private conversations between students and faculty, to name a few functions.
Students may be some of the last people to think about the safety of their personal data, but much can be risked by disclosure of medical conditions, sharing of personal situations, and other manner of sensitive communication these services enable. Hackers now have possession of names, emails, course info and private messages, facilitating incredibly convincing phishing schemes for future access. All students and staff whose data was exposed should keep watch as potential targets of social engineering, AI generated scams and phishing attacks.
More than 8,800 institutions across 50 countries have been exposed in this breach. K-12, secondary and even medical schools (and thus healthcare institutions): all were swept up. Learn more about the critical importance of medical device encryption and security in our white paper.
The latest twist in the tale is that Instructure has just reached a deal with ShinyHunters to prevent the publication of the 3.65 TB of stolen data. Paying the ransom is always an option for an extorted company, and Instructure claims all the data was returned to them and that they received confirmation that the stolen cache has been destroyed. Whether this is any kind of guarantee for those affected is for them to decide.
Now, this breach is currently a major story of the nefarious digital crimes of ShinyHunters. Another comes courtesy of Europe’s cybersecurity agency, CERT-EU. The agency accuses the hacking group called TeamPCP of stealing 92 GB of data including names and email addresses/messages from the European Commission, the EU’s highest executive body.
Curiously, though, it was ShinyHunters that shared the data online. Funny enough, a member of the group, speaking to TechCrunch explained that they themselves had pilfered some of the stolen data from TeamPCP and posted it.
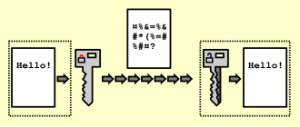
Regardless of who is responsible for which part, the agency warns that 29 other EU entities may be affected, and dozens of internal clients affected by data exposure. Both incidents also involve stolen API keys associated with the relevant accounts – both AWS and the API keys Canvas uses to connect to external applications. In our efforts to combat data theft via strong encryption, NetLib Security’s Encryptionizer solution gives organizations the means to administer encryption policies and manage their keys from a single interface – to control encryption across geographically distributed physical, virtual and cloud environments.